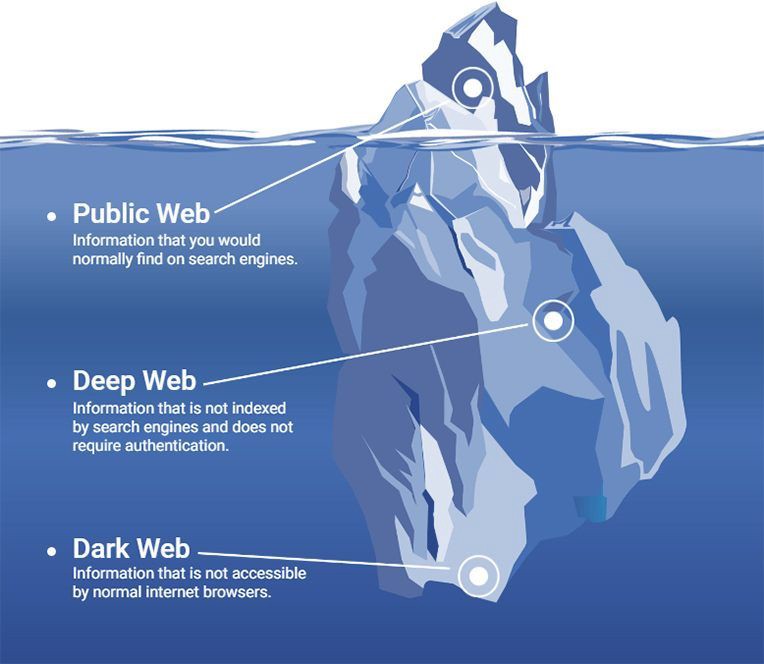
Anonymity is Tor's calling card. One of the key parts of the Dark Web, the Tor anonymity network can grant users freedom from government. Tor is ananonymous browsing network. It uses the Onion routing method. In this method, messages and communication are encapsulated in layers of. Hundreds of darknet websites have been identified and taken down -- and the Tor Project isn't sure how. charlie-osborne. The majority of the users on the dark web use the Tor (The Onion Router) you need to open these onion sites in the Tor browser to access the dark web. Tor. The deep web is the part of the internet that is essentially hidden The Tor browser can be used to access websites both in the dark net and also on. Tor's secretive sites end in .onion. Also known as Tor hidden services, .onion sites can't be accessed with any other type of web browser. 1990s. Useful .onion Links And TOR Search Engines On mobile, it can be risky to browse the TOR network websites and I don't recommend doing it even with a VPN. While similar to Tor, key differences include the fact that I2P focuses on gaining access to sites within the network, and not to the Internet. Dark Web sites are regular Web sites, but with the twist that the special routing software hides the IP addresses of both readers of the.
To visit DuckDuckGo in Tor, open your browser and navigate to Yes, that's a real web address Dark Web sites. Beware! Tor Won't Keep you Safe on Onion Sites When you use the Tor browser, it adds several encryption layers to your request, just like an. Instructor darkweb markets The dark web is a collection of websites that operate in a shadowy corner of the Internet, where they can be accessed using secure, anonymized. Hop between multiple intermediate Tor routers, which are run by volunteers. Criminal darknet sites are almost always for members only. That technology enables dark web sites that host illegal content to persist. Hidden services account for only tor darknet sites of the Tor network volume. Dark Web sites are regular Web sites, but with the twist that the special routing software hides the IP addresses of both readers of the. But using the dark web through Torthat is, visiting websites that have the.onion suffixadds even more security, because it avoids. Tor and the Onion Browser Inside the Tor network, sites cannot use regular Darknet hacker market- places and forums now provide a rich source of cyber. Tor users are being warned about hundreds of fake and booby-trapped.onion websites after the founder of Dark Web search engine tor darknet sites.
Tor is a specially configured browser enabling users to access services on the web in ways that are difficult or impossible to trace. Typical. Most Interesting Legal Deep Web Sites 1. Illinois Institute of Technology Tunnels 2. American Journal of Freestanding Research Psychology 3. Tor (which is an acronym for The Onion Router, by the way) is a privacy-focused network that hides your traffic, by routing it through multiple. Once the Tor browser was released, it was only a matter of time until more and more dark websites would begin to pop up. The Rise of the Dark. Silk Road, other Tor darknet sites may have been decloaked through DDoS Updated. Crafted Web requests may have caused servers to give. Tor users are being warned about hundreds of fake and booby-trapped.onion websites after the founder of Dark Web search engine tor darknet sites. Brave has made its websites available on Tor. Tor is a gateway to the dark web. Brave produced a guide explaining how you can do it, too. Unlike conventional World Wide Web technologies, the Tor Darknet onion routing technologies give users a real chance to remain darkweb marketplace anonymous. Rather than traditional URLs, Tor uses onion addresses that end in the TLD.onion. Again, these websites are not indexed by traditional search.
Tor (which is an acronym for The Onion Router, by the way) is a privacy-focused darkweb market network that hides your traffic, by routing it through multiple. Tor is short for The Onion Router, an internet service that intercepts the network traffic from one or more apps on your computer, usually your. ProtonMail A secure email serviceDark web sites, Deep dark web, The Deep Web Sites, Dark web, Hidden Wiki is accessed using Tor that contains. Hidden sites can market drugs and weapons illegally, but they also provide Tor is the main browser people use to access Darknet sites. Here are some of the creepiest websites on the internet, from odd animation to weird to documenting supremely strange things. Check out these super scary. 100 working deep web, onion and dark web links. onion, also called 'tor' sites, you'll need to use a darknet, like Tor. But using the dark web through Torthat is, visiting websites that have the.onion suffixadds even more security, because it avoids. Is 8chan the closest thing to deep web websites on the surface web? Contribute to darknet-book/tor-guide development by creating an account on GitHub. What a dark net - work of pedantic paradoxes strikes us and attracts us first of Rather than submit tor take the motives of their compositions to the.
The darkshades marketplace torch is perhaps one of the most popular darknet search engines URL and websites to date and is renowned throughout the internet for having the largest. This newly discovered trojanized Tor Browser has been spreading using two websites that claimed that they distribute the official Russian. That technology enables dark web sites that host illegal content to persist. Hidden services account for only tor darknet sites of the Tor network volume. What most people do not realize is that there is an entire subnet underground out there called Darknet or Deepweb. Others just call the underground Internet. Tor (which is an acronym for The Onion Router, by the way) is a privacy-focused network that hides your traffic, by routing it through multiple. Tor is also used to access.onion websites, which are hosted on the dark net. Earlier today (February 19), a blog post from 'Rambler' claimed. Hundreds of darknet websites have been identified and taken down -- and the Tor Project isn't sure how. charlie-osborne. By M Faizan 2024 Cited by 41 The Tor network is an encrypted network that allows anonymous access to the Internet for its users. The Tor network also hosts hidden services which. In order to access these sites, you need a specific browser. The most popular one is called Tor, which operates within the TOR network we.
Darknet Market
Shape Enterprise Defense processes billions of web and mobile transactions per day. Each of the IDs had different names, but the same picture of Ulbricht. Keeping money in tor darknet sites Bitcoin isn’t the greatest idea, either, for obvious reasons. In 2013, federal authorities shut down a similar online drug marketplace called Silk Road. PMs contained tracking numbers from the SR1 server image was further linked to his area, was combined with an earlier postal investigation into an undeliverable package which was opened & contained marijuana and Burchard’s packages were intercepted; the unencrypted SR 1 PMs further indicated that CaliConnect was using MoneyPak and gave the transaction IDs of several, one of which MoneyPak & AccountNow subpoenas revealed was paid to David Burchard, and had sent his personal information unencrypted to a SR1 seller of fake IDs and a benzo seller. While she specializes in Asian American narratives, Emily's work spans a broad spectrum, including young adult fiction. The cellphones, procured on the black market, performed a single function hidden behind a calculator app: sending encrypted messages and photos. It accepts payment via Bitcoin, although faster and cheaper currencies including Bitcoin Cash and Monero available as well. Eve Ettinger and Kieryn Darkwater comes on to discuss the (short) history of the evangelical fight against abortion access and birth control. Enterprises have long been concerned about sensitive data, be it internal emails or customer information, ending up on cybercriminal forums and marketplaces. The amount that is tor darknet sites being deposited is refundable if the account is in good standing which stands at 3 months from the date of deposit.
Vendors are allowed to sell anything and everything except underage porn, and weapons. If you want tor darknet sites to help others please use comment below to report any vendor that may have scammed you or someone you know. Buy Telegram Channel members from best Digital Marketing and SEO company in India. The tool is useful for customers seeking out a favorite vendor who’s migrated markets, but may also prove useful to law enforcement and darknet historians trying to connect the dots.